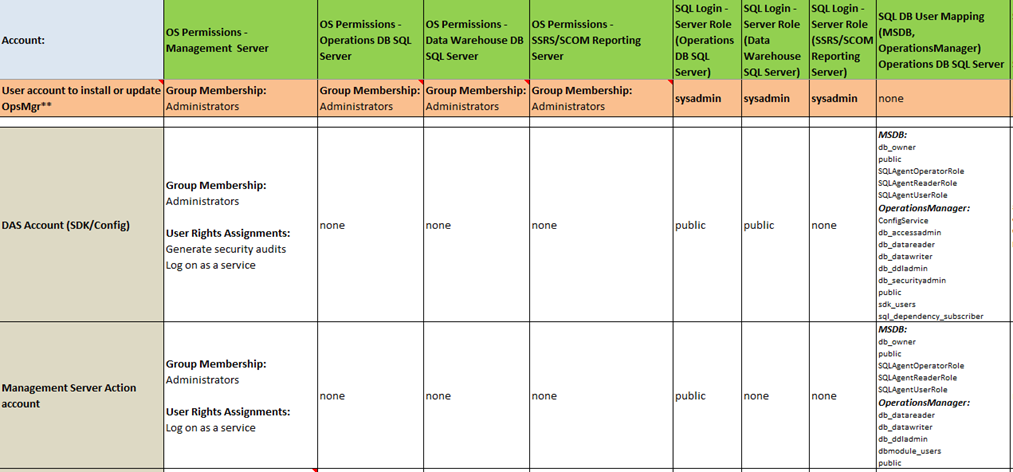
Below you will find a security account matrix for SCOM 2016, that includes all the common security accounts in SCOM, and their default or recommended permissions. This includes the management servers, the database servers, SQL Role permissions, and database mappings. You can use this to correct deployments where permissions got modified incorrectly, or to verify that a least privileged model is being used.
Download: https://kevinholman.com/files/SCOM2016_Security_Matrix.xls
Example:
This download is for SCOM 2016. For SCOM 2019 please see: https://kevinholman.com/2020/07/23/scom-2019-security-account-matrix/

Hello Kevin,
Once again thank you for another helpful post!
But the link is broken.
Fixed, thanks!
Hi Kevin,
The Link is not working for me.
I receive an: Oops! That page can’t be found.
Regards Menno
Fixed, thanks!
Thanks for the update. Just to confirm, does this apply to SCOM 2019 as well?
Thanks.
No – I will be publishing a new document for that.
Any idea when that document will be published?
Thanks
Hi Kevin,
Can you please publish the document for SCOM 2019
Hi, also valid for 1807?
Should be.
Hi ,Can you clarify why SCOM accounts needs DBO & SQL Agents roles on MSDB. Does the product create jobs and manage it. Is this access mandatory since those are manage by DBA’s and access not granted to application account. Please help.
DBO is no longer required. See the latest at: https://kevinholman.com/2020/04/04/ur9-for-scom-2016-step-by-step/
Yes – SCOM does create jobs, then delete them, as we use the SQL agent to adjust schedules for maintenance mode. This access is likely not mandatory, since it will only break schedule maintenance mode. For scheduled maintenance mode feature to work, it is mandatory. Note – in SCOM 2019, this access is configured during setup by default.
Pingback:Implementing gMSA in SCOM 2019 UR1 - The Monitoring Guys
Can you use Local System as the action account on a gateway server? We don’t use the action account for agent deployment, so we don’t need it for that.
Absolutely. I ONLY use Local System for gateways, unless the customer has a VERY good reason to use a service account. We need to get away from service accounts.
Hi Kevin,
is it possible to get security matrix for SCOM 2012 R2? Thanks