Well, sort of, anyway. ![]()
Quick Download: https://github.com/thekevinholman/SNMPDiscoveryFromCSV
I have written on SNMP monitoring in SCOM a few times:
https://kevinholman.com/2015/02/03/snmp-trap-monitoring-with-scom-2012-r2/
https://kevinholman.com/2016/04/20/writing-a-custom-class-for-your-network-devices/
This one will be a little different.
One of the challenges I have heard many times with SCOM – is that we must discover a network device, in order to monitor or receive SNMP traps from that device.
This can be a big problem for customers, as they often have network devices that only sent traps, but are not query-able via SNMP GET requests. If we have challenges getting a network device to discover in SCOM, we can’t generate an alert or collect the trap.
Let’s make that a little simpler. This article will demonstrate how we can create a new class for our network devices, discover them from a simple CSV text file, and then monitor them for SNMP traps.
This post will be based on the old SCOM 2007 SNMP libraries, which are still included in SCOM for Backwards Compatibility.
This uses the System.SnmpTrapProvider System.SnmpTrapProvider | Microsoft Learn
The idea is to create a management pack with the following:
1. A new Resource Pool, that will host our network devices and load balance them.
2. A Class that will define our SNMP network device and any properties.
3. A discovery, which is a PowerShell script to discover our network devices.
4. Rules, to alert on all traps, specific traps from a specific OID, and specific traps where a SNMP varbind contains specific data
Therefore – even if you don’t need this functionality – this will be a very good MP example, of discovering objects from a CSV, and having those objects hosted by a resource pool and load balanced by resource pool members!
Our class definitions look like the following:
<ClassTypes> <ClassType ID="SCOM.SNMP.Device.Class" Accessibility="Public" Abstract="false" Base="System!System.ApplicationComponent" Hosted="false" Singleton="false" Extension="false"> <Property ID="DeviceName" Type="string" AutoIncrement="false" Key="false" CaseSensitive="false" MaxLength="256" MinLength="0" Required="false" Scale="0" /> <Property ID="IP" Type="string" AutoIncrement="false" Key="true" CaseSensitive="false" MaxLength="256" MinLength="0" Required="false" Scale="0" /> <Property ID="SNMPCommunity" Type="string" AutoIncrement="false" Key="false" CaseSensitive="false" MaxLength="256" MinLength="0" Required="false" Scale="0" /> <Property ID="SNMPVersion" Type="string" AutoIncrement="false" Key="false" CaseSensitive="false" MaxLength="256" MinLength="0" Required="false" Scale="0" /> <Property ID="Description" Type="string" AutoIncrement="false" Key="false" CaseSensitive="false" MaxLength="256" MinLength="0" Required="false" Scale="0" /> <Property ID="Owner" Type="string" AutoIncrement="false" Key="false" CaseSensitive="false" MaxLength="256" MinLength="0" Required="false" Scale="0" /> </ClassType> <ClassType ID="SCOM.SNMP.Device.ResourcePool" Accessibility="Public" Abstract="false" Base="SC!Microsoft.SystemCenter.ManagementServicePool" Hosted="false" Singleton="true" Extension="false" /> </ClassTypes>
There is a datasource for the Resource Pool, and a Discovery for that as well, but those aren’t important here. They just create the pool and load the relationship so the pool will host our devices.
Then – there is a discovery that discovers against the CSV file and creates our instances:

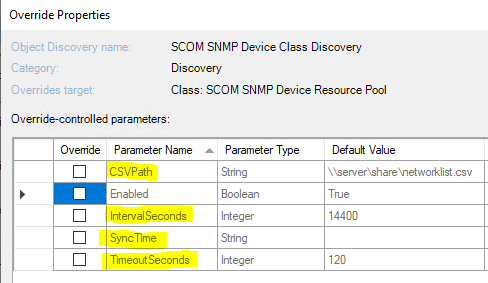
You can override this for Interval, SyncTime, Timeout, and the CSV path you want to discover from:
My example CSV is very basic – you can add or remove fields you want to discover. For my example I include the device name, IP, Base64 SNMP Community String, a description, and the Owner. You may change these as you wish, but you have to change the discovery script as well if you do.
We require a DeviceName, IP Address, SNMP Community String (base64), and SNMP Trap version at a minimum:

You must provide the Community String in Base64. To convert your community string to Base64 – use PowerShell.
Here is an example for a community string of “public”:
$CommunityString = 'public' [System.Convert]::ToBase64String([System.Text.Encoding]::UNICODE.GetBytes($communityString))
You must provide a SNMP Trap version, either “1” or “2” depending on how your device sends traps. Even some SNMP v2 devices default to SNMP v1 traps.
This will discover your objects:

And let you generate alerts when traps are sent to the SCOM Management server that hosts these objects:

I have included three different rule examples:
-
A rule to alert on ANY trap sent from the device.
-
A rule to alert on ANY trap sent to the device that comes from a specific OID.
-
A rule that will filter a specific payload in the trap, such as data in a specific Varbind.
You can look at the rule configurations to better understand this method, to start creating your own rules.
This MP contains a Resource Pool dedicated for these devices. You must configure this, as by default it will use Automatic membership, and distribute your network devices across all management servers. This means each device must send a trap to EACH management server in the pool, because we do not control which management server hosts the device. For this reason, especially for testing, you may want to set the Pool membership to manual, and limit the management servers. Many devices are only able to send traps to two IP destinations, so it would be wise to choose two management servers for pool membership – to give high availability and load balancing, or just one management server for simplicity and testing:


So with a simple CSV, we can quickly “discover” our network devices, and start getting traps from them really quickly.
You can download the example management pack and sample CSV file here:

If you were doing this type of SNMP discovery for devices/appliances that are Windows based, would you also need to edit the ic-post-processor.asl file (mentioned in you blog “How to discover a Windows Computer as a Network Device in SCOM 2012”)?
That would not be required as these will not be objects of the “node” class nor use the built in SCOM discovery mechanism.
Thanks Kevin. Since this doesn’t use the SCOM discovery mechanism, is there a need to have the Windows OS SNMP services turned on to receive the traps?
I am pretty sure it does not. I never use those.
how could this work using SNMP v3
SCOM is not capable of handling SNMP v3 traps.
Hi Kevin,
We have discovered vCenter 6.5 version in SCOM 2016. We added them using both the methods (i meant SCOM discovery and Without discovering the SNMP Device). and udp ports 161 and 162 are also open between source vcenter to SNMP SCOM Receiver server. We could capture the test trap by wireshire running on SCOM SNMP Reciever Management Server from vCenter. But this trap is not captured by SCOM. We already created test trap capturing rule and test trap events capturing rule. All the traps are captured from various devices but from this vCenter it is not capturing. We removed the version line also in the discovery as you suggested.
Hi Kevin ,
I would like if you can share this link again https://blogs.technet.microsoft.com/brianwren/2009/01/21/snmp-queries/ is not working and I can not discover a community that is not public, thanks in advance.
Regards
Diego Rios.
Hi Kevin, I followed the same steps but devices are showing un-monitored in health explorer.
Thats by design, and a fundamental understanding of SCOM. Unmonitored means simply there is no health state from MONITORS targeting that class. If you discover a class, and only target rules at it, it will always have no health state… by design. Rules and monitors are different.
Thanks Kevin for replying. I am able to receive traps from Lenovo server. but how could i set it for limited set of OIDs.. How to get the OIDs details? Please let me know if you have any published anything for it.. Thanks for your help Kevin.
Hello Kevin,
I need to configure Hitachi monitoring and the problem is G600 devices have no name defined in AD (nslookup doesn’t show any name).I just have an IP of Hitachi controller from which SNMP are sent and in wireshark I can see SNMP packets coming through to MS. How should I proceed if the device name doesn’t exist?
Hello Kevin,
Using Community String for SNMP device is vulnerable as per organizational policies, hence we are advised to use SNMP V3 which is using credentials based authentication or device identification. So how do we proceed with this scenario ?
This is a great article, surprised that more like this don’t seem to exist. Please can you advise on how to do this for SNMPv3. thanks
Does this work with Windows 2016 and SCOM 2016. We cant for the life of us get it to work. Discovery works fine and devices are listed, Community string is base64 as per article, resource pool is statically set to one server. Wireshark on SCOM server shows traps being received on port 161 as Version 1 and type TRAP. However, nothing is displayed in the Alerts?
We have confirmed on SCOM server port 161 is bound to snmp.exe (Windows SNMP Service) and 162 is bound to MonitoringHost.exe (SCOM Agent) . We even set the community string in the Windows service settings to see if this made a difference. Any ideas?
thanks
Ok, we have it working now.
For other that struggle
– Ensure you use same community string as shown in this article – nothing else works
– Ensure your SNMP Trap sending device is configure to send traps to port 162
– Ensure your SNMP Trap sending device is configured to use SNMPv2
– Ensure port 162 is bound to MonitoringHost.exe (netstat -abn)
thanks again to Kevin for taking the time to share this
Hello,
first of all thank you for this management pack. At first everything worked fine, but then I got the following event on one of 2 ressource pool servers:
EventID 5399 A rule has generated 50 alerts in the last 60 seconds. Usually, when a rule generates this many alerts, it is because the rule definition is misconfigured. Please examine the rule for errors. In order to avoid excessive load, this rule will be temporarily suspended until …
Rule: Demo.SNMPDevice.AlertOnAnyTrap.Rule
Since this event appeared days ago I do not get any SNMP Traps from any source. Have anyone an idea how I get this management pack working again. Is there a way to see if the rule is still suspended?
Thanks
Hi GV,
Do you have any idea how I can make sure ‘Ensure port 162 is bound to MonitoringHost.exe (netstat -abn)’
Alerts are still not coming through for me at all.
Hi again,
So I have managed to get port 162 is bound to MonitoringHost.exe, however, I am not getting any alerts to come to the console. WireShark is showing traps arriving at the SCOM server.
I have setup as mentioned by GV above.
– Ensure you use same community string as shown in this article – nothing else works
– Ensure your SNMP Trap sending device is configure to send traps to port 162
– Ensure your SNMP Trap sending device is configured to use SNMPv2
– Ensure port 162 is bound to MonitoringHost.exe (netstat -abn)
Any idea why I am nit getting any Alerts?
Kind Regards,
Chris
For anyone looking to download the Example Management Pack, you can also find the Technet Article here:
http://web.archive.org/web/20200318054423/https://gallery.technet.microsoft.com/SCOM-Management-Pack-to-ac659c99
Download Link:
http://web.archive.org/web/20200318192615/https://gallery.technet.microsoft.com/SCOM-Management-Pack-to-ac659c99/file/181622/1/Demo.SNMPDevice1.0.0.1.zip
Updated article with correct links to Github where all my content is.
Hi Kevin,
I have followed your blog and got the SNMP ( Dell Open Manager Device) discovered very quickly. But alerts are not reaching the console. I have made sure that the SCOM IP is configured with correct community string on both sides.
Any idea why alerts are not reaching in SCOM ?
For anyone having issues with this Management Pack not alerting for you when you have everything configured correctly, try enabling the SNMP Trap service on your Management Server. This fixed my customers issue with this MP.
If you are trying to create another rule for this MP, you will have to edit the MP XML Manually to add the functionality you are looking to achieve.
The SCOM Console UI does not allow the ‘Snmp Trap (Alert)’ rule type to target any other class than the ‘Node’. So the default ‘Demo SNMP Device Class’, will not allow you to save the rule. You will see an error like this:
—————————
Error
—————————
The targeted object is not valid for an SNMP rule or monitor. Select an object that is either a network node or a component that is hosted on a network node.
—————————
OK
—————————
The SCOM Source was updated in newer versions of SCOM to force the ‘Node’ class as the Rule target on this Rule type.
Hi Kevin,
Followed this to a T but have one issue, my csv contains my apps/systems I want to process traps from some of which have the same IP (because I have multiple apps running on the same system). When SCOM processes the CSV, it only “discovers” the unique IP’s – how can this be resolved?
Thank you,
Bryan
Hi,
Must the IP’s in the CSV be unique? I have a csv created that contains 142 unique names some of which, point to the same IP but only the unique IP’s are discovered by SCOM – any idea what would cause this?
Hi Kevin,
I’m wondering if you don’t mind if I pick your brain re: this topic in your post.
Firstly, I have SNMP configured in SCOM with 2 resource pools, 3 x MS in each resource pool, managing SNMP devices successfully, lots of devices discovered and several Custom SNMP MP developed with rules alerting on Traps so there is no issue here.
Task in hand now is I need to monitor Cyber Ark (CA) application via SNMP. The product is installed a on a Windows server, and the server hardened, so essentially makes it an appliance, hence no agent is allowed. I discovered the Windows server with SNMP into SCOM, and confirmed Windows coldStart and LinkUp Traps are received into SCOM, however the CA Traps are not being received into SCOM. I know the CA Traps are reaching all the MS in the pool with Wireshark on each MS.
So then I deleted the Windows server from SNMP Devices and tried your method of alerting on SNMP Traps in SCOM without Discovering the SNMP device. I have the server in SCOM using the Demo.SNMPDevice.xml and csv, and in the pool that the Demo.SNMPDevice.xml creates I added the same MS from the Resource Pool I have, CA SNMP is only configured to send to these 3 MS. Again the traps are not received into SCOM or by the rules in the Demo.SNMPDevice.xml MP catch all rule or by the rules modified with CA OIDS, or by a separate ‘process all Traps MP’ from one of your other posts which is working okay, but again I know the CA Traps are reaching all the MS in the pool with Wireshark on each MS.
Have you come across this where Traps are not coming into the Console but are reaching the SCOM MS as seen in Wireshark? Just to reiterate here I know SCOM is configured correctly, as receiving Traps for many other devices.
The one thing I noticed which is odd, is I don’t seem to see a SysOID in the MIB for the CA application so the CA application itself does not appear discoverable via SNMP, it’s just an application with SNMP running allowing outgoing Traps on a Windows server, and does not use 161 so unable to poll the application, but I figured by using the Demo.SNMPDevice.xml and getting the device this way into SCOM it shouldn’t matter just to receive Traps into SCOM.
https://cyberark-customers.force.com/s/article/00003577
https://docs.cyberark.com/Product-Doc/OnlineHelp/PAS/11.4/en/Content/PASIMP/Configuring-Remote-Monitoring.htm?Highlight=Configure%20Remote%20Monitoring
Hi Kevin,
I have figured this out and got it working so no need to reply. Cyber Ark Traps are being received into SCOM.
Thanks for your post.
Graham
Hi Graham,
I know this is a very old post and hoping that you might be able to shed some light. Can you please provide a quick run down of how you setup the process of monitoring the CA vault. I have followed the steps form other articles of Kevin.
Hi mate,
Could this MP be connected to an existing Resource Pool instead of creating a new one in the MP?
Graham.
Hi,
has anyone got it working with SNMP v3 ?
I’ve used this MP to create a good VMware Management Pack. I was going to use this MP to create a Netapp Storage Management Pack but the Netapp Team only want to use SNMPv3 which I have seen from someones response this MP will Not work with SNMPv3. Does anyone know of a similar MP to this that will work with SNMPv3 or is there a way to modify for this MP to get it working with SNMPv3
Hi Lee – I’m looking to do exactly this as our VMware vCenters are now appliances. Can you share how you got it working? Thank you!
That is so odd. I am getting the packets on the NIC on my management server, but the rule does noot generate any alerts. Instead the following is seen in the event logs:
— Event 11003, Health Service Modules, “Error registering Snmp Traps Status Trap register failed..” and then the rule gets unloaded. I tried iwth the SNMP Trap Service on and off, does not matter. I also get lots of:
— Event 12193, Health Service Modules, “Error: Trap service failed to register the trap %5. Details: %6″…
Any ideas what I am missing?
I am assuming the rule unloads long before any traps are actually sent, like as soon as the rule tries to initialize? What’s special about the rule?
HI Kevin,
thanks for taking time to reply, really appreacite it. The rule unloads indeed . The rule is actually from the SCOM.SNMP.xml, the one, which alerts on all OIDs – “SCOM.SNMP.Device.AlertOnAnyTrap.Rule”.
I tried with the SNMP Trap service off and with it being “Running” as Blake suggested in the comments. In both cases I get those Events in the OpsMgr event log. The strange part is that in XML details of the 12193events I see this strange error string: “”. Already tried using ProcMon, restarted service (MMA, SNMP Trap, etc.) no single “Acess Denied” there.
Currenty a bit desperate as this is my last resort of getting SNMP Trap from special Systems I cannot dioscver otherwsie.
Thanks in advance for all your inputs!
The error string is: “-E-zWSAEACCESS-Permission denied”
An update to the issue and a lesson learned: Don’t create customer Firewall rules for the SNMP Ports (162, 161), but use the Built-In rules (Operations Manager SNMP Response, Operations Manager SNMP Trap Listener) instead – there is a huge difference.
Hi Kevin
This works great with trap and rules for many devices, however can you extend the the MP (and three rules) with an catch all monitor sample to show it can work too
Some systems sends a OK trap again when it is OK again (e.g. disk is in warning, disk is normal)
Hi Kevin,
I am just trying to configure a test trap for APC and Eaton UPS device from SCOM.
SCOM is already integrated with Service now, however when i do a test trap from the above device its not creating any alerts in SCOM which in turn should create a ticket in SNOW.
Is there any way we can create a rule for the test trap to make it functional.
Hi Kevin,
have you tested the MP by configuring a GW in the Resource Pool? I did a test with 1x GW in the RP, disabled the default observer as recommended and noticed an event on the GW that says that the RP Device Relationship discovery fails with an exception. The exception shows that a bunch of .dlls cannot be loaded and those are only present on Management Servers. So I would assume that the solution works only when you have real Management Servers in the RP? Can you please confirm this?
Thanks for the amazing solution and for your efforts!
I have not. This is interesting, I have seen scenarios where GW are missing specific DLL’s and cannot function for specific workflows, but I have not seen where they cannot even join a resource pool. I haven’t tested GW in a RP in quite some time.
I have setup as mentioned by GV above.
– Ensure you use same community string as shown in this article – nothing else works
– Ensure your SNMP Trap sending device is configure to send traps to port 162
– Ensure your SNMP Trap sending device is configured to use SNMPv2
However, for configuring port 162 is bound to MonitoringHost.exe I need additional information.
Specifically how is this done?
Hello Kevin,
I managed to get the discovery working. It now shows the Server Name, IP, and owner. It does not show SNMP Community String or Description in SNMP Devices. What am I missing?
I did get Port 162 to show bound to MonitoringHost.exe
Could this also work on gateway servers?
To everyone struggling to get this working, I’d like to emphasize the importance of using the community string Kevin is using. I’m not exactly sure of the mechanics behind it, but while being sure everything was configured correctly, all other community strings did not give any result.
Tldr;
Don’t be stubborn like me, use the community string as shown in the article.
Thanks Kevin. Discovery completed and device details are in the SNMP devices. But when we do test trap sending to MG server not receiving in the alerts. can you guide any other troubleshoot steps to configure.