Quick Download: https://github.com/thekevinholman/SCOM.Management
This is a Management Pack that eases the administrative burdens in SCOM. It allows you to have a lot of handy discovered properties, and includes tasks that allow you to delegate administrative actions to your users. It also serves as a good example MP on how to write classes, discoveries, and most importantly many task examples for command line, VBscript, and PowerShell.
I didn’t write all these – a bunch of ideas came from Jimmy Harper, Matt Taylor, Tim McFadden, Daniele Grandini, Raphael Burri, Brian Barrington, Patrick Donovan and their feedback + MP examples. This was more of an effort to combine lots of useful administration in one place.
This MP creates a folder in the console with some views for Agents and Servers. It includes a view for the custom agent class properties (SCOM Agents) along with custom class properties for Management servers and Gateways (SCOM Servers). It also includes views for Health Service and Health Service Watchers, for specific tasks that apply to those classes.

First – useful discovered properties:
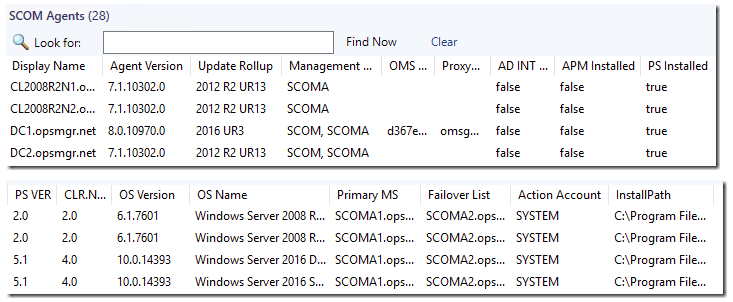

The “real” Agent Version
The Update Rollup level of the agent
If Active Directory Integration is enabled or not for the agent assignment
Any Management Groups that the agent belongs to. This is nice to see for old management groups that get left behind.
Any Log Analytics (OMS) Workspaces the agent reports to.
Any Log Analytics (OMS) Proxy URL if configured.
A check if PowerShell is installed and what version. This is important because PowerShell 2.0 is required on all agents if you want to move to SCOM 2016.
CLR .NET runtime version available to PowerShell
OS/CPU Architecture (AMD64 or x86)
OS Version and Name
Primary and Failover management servers. I am getting this straight from the agents config XML file, sometimes agents might not be configured as you think – this is from the authoritative source…. what’s in that specific agents config.
The default Agent Action account. Helpful to find any agents where someone installed incorrectly.
The agent install path.
If the APM services are installed with the agent, or if the Agent was installed with NOAPM.
If the agent uses a Certificate for Healthservice communication, along with Cert Expiration, Thumbprint, and Issuer.
The Agent IP Address
The Port connectivity availability status (Connection) of agents to an array of MS and GW servers to test for firewalls
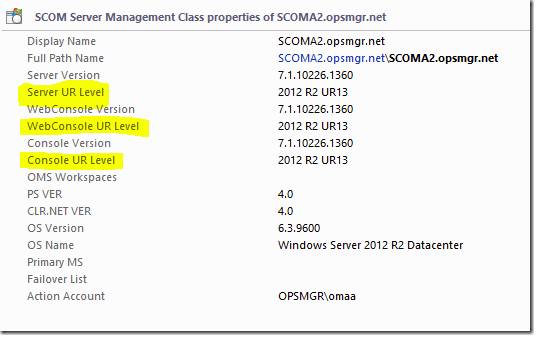
Also I added server discovery of properties (Management Servers and Gateways):


Next up – the tasks:
SCOM Agent tasks:

One of the problems with tasks, is that they are scoped to a specific class. Some cool tasks are attached to Windows Computer, some to HealthService, some to specific app classes. Or – people write tasks and scope to System.Entity. This places the task in ALL views. That’s handy, but if everyone did that we’d have an unusable console for tasks.
Agent – AD INT DISABLE (and ENABLE) – this task will enable or disable AD integration for agent assignment, and restart the agent.
Agent – DELETE – This allows your end users to DELETE agents from SCOM if they should no longer be monitored.
Computer Management – duh.
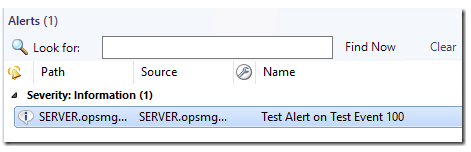
Create Test Event – this task creates event 100 with source TEST in the app event log, and there is a rule in the MP to generate an info alert. This will let you test end to end agent function, and notifications.
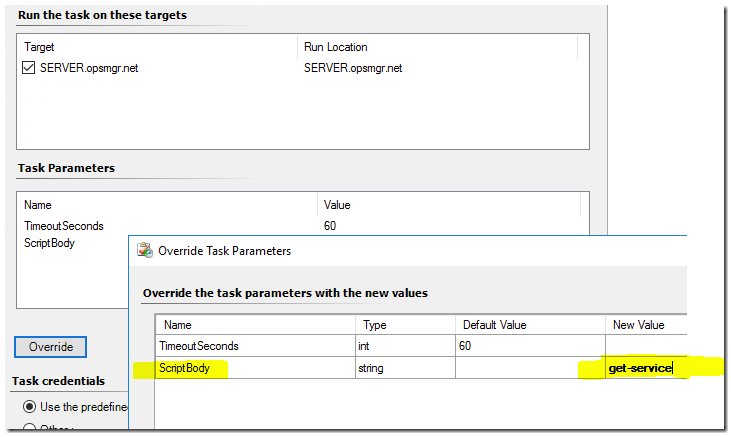
Execute any PowerShell – this task accepts one parameter – “ScriptBody” which allows you to pass any PowerShell statements and they will execute locally on the agent and return output:

Execute any Service Restart – this will take a servicename as a parameter and restart the service on any agent on demand. You should NOT use this for the Healthservice – there is a special task for that:

Execute any Software from Share – this task will accept an executable or command line including an e4xecutable, and a share path which contains the software, and it will run it locally on the agent. This is useful to install missing UR updates, or any other software you want deployed. This will require that “Domain Computers” have read access to the files on the share.

Export Event Log – this task will export any local event log and save the export to a share. It will require that the “Domain Computers” have write access to the share.

HealthService – FLUSH – This task will stop the agent service, delete the health service store, cache, and config, and start the service back up, provoking a complete refresh of the agents config, management packs, and ESE database store.
HealthService – RESTART – This is a special task which will reliably bounce the HealthService on agents using an “out of band” script process. Many scripts to bounce the agent service fail because when the service stops, the script to start it back up is destroyed from memory.
HSLockDown – LIST Accounts, and HSLockDown – Add SYSTEM. These will list the accounts configured under HSLockdown and will also add Local System back if desired.
Management Group – ADD and Management Group – REMOVE – these are script based tasks to add or remove a management group from an agent
Log Analytics (OMS) Workspace – ADD and Log Analytics (OMS) Workspace – REMOVE – these are script based tasks to add or remove Azure LA workspaces and configure a proxy for direct internet or OMS Gateway. You can also choose your Azure Cloud Type – 0 (default) for Commercial Azure Cloud, or 1 for US Government Cloud.
Ping – (Console Task)
Remote Desktop – (Console Task)
SCOM HealthService Tasks:
This is a special task that will allow you to set agents back to “Remotely Manageable” instead of having to edit the SQL tables!
SCOM HealthService Watcher Tasks:

The “Agent – Delete” task is really cool. It allows an operator with access to the task to be able to clean up (DELETE) agents from the SCOM console – without having access to the Administrator role. This task will run on the management servers and delete agents (this is a Delete – not an uninstall) This is handy for cleaning up old agents that are not present anymore.
SCOM Server Tasks:

I have included “Agent – INSTALL” and “Agent – DELETE” tasks, targeting the management servers. These will allow you to push installAND delete SCOM agents from the Operators console. You simply need to Override the task and proved the computers FQDN:

In order for this task to work – it will attempt to push the agent as the SCOM Management Server Action account. You will need to grant that account administrative rights on your server in order to be able to use this.
Do you have other useful agent management tasks that you think should be in a pack like this? Or discovered properties that are useful as well? I welcome your feedback.
Warning: Some of these tasks can be considered “risky” to deliver to your Operators, like exposing the ability to execute any PowerShell, restart any service, and install any software from a share. If those are things you don’t ever want exposed in your SCOM environment – then delete those tasks from the MP, or do not expose them in your non-administrator scoped console access.
Download the MP here:
https://github.com/thekevinholman/SCOM.Management

The discovery on gateways is not correct if you run version 1807, it still shows UR level 1801 in the version 7.0.063 of this pack.
That’s because the file being checked ‘HealthService.dll’ is not changed.
When you replace HealthService.dll to MOMAgentManagement.dll on line 1615 of the pack it does show the correct UR Level version, but i don’t know if that’s ok for older scom versions.
Yeah, I have been really lazy about fixing 1807. I don’t want to mess with it since SCOM 2019 is coming out soon. 🙂
I hope real soon 🙂 1801 was released early February last year – I’m excited to see all the hard work of 1901!
would be nice to add a new column in Agents view to obtain maximumQueueSizeKb value
key: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlsSet\Services\HealthService\Parameters\Management Groups\maximumQueueSizeKb
Here is my personal opinion on that.
I almost *never* adjust it. If you need to adjust it – that means your MP is doing something bad, and I’d rather attack the MP. If the default queue size of an agent isnt big enough – then something is wrong. Too many times support has done this as a band-aid solution to the real issue. Allowing a bigger queue is almost always a bad thing. It means we are allowing MP’s to discover too much data, or workflows to output too much data. I’d rather focus on making the MP better. There are rare occurrences where I’d adjust this (like for VERY specific and well written 3rd party MP’s which need it for VERY specific reasons) but these are atypical.
So, that being said – this is just my personal experience with my customers. Why do you adjust it in your environment?
Considering your viewpoint that it should not be changed (except in rare circumstances), perhaps it would be helpful to add the column anyway so that any agents with modified/custom queue size can be identified easily and reviewed. This might be useful when there are numerous admins chef-ing in the kitchen.
Easy for me/us to suggest tasks that create more work for you. 😉
Thanks for all of your contributions!
If someone just HAS to have that in a view, they need only click one view down in this MP – “SCOM HealthService” – as this is already a discovered property of the Healthservice class.
I know this is many years later, but is the property value shown as “Maximum Queue Size” actually the same as “HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlsSet\Services\HealthService\Parameters\Management Groups\maximumQueueSizeKb”?
We have had to test changes to this entry for a current MS service ticket, but on most servers, the value is “15360” and the “Maximum Queue Size” in the applicable Microsoft.SystemCenter.Agent class object is “104857600”
So one issue I found when I was trying to dual home machines from my current prod 2012 to my pre prod 2016 if I selected a group of machines and there was a single machine in there I did not have access to with the account I was using it would fail the entire group. Is there a way to have the rest work and only the one that I do not have access to fail?
Not that I am aware of. It seems to be a side effect of SCOM tasks and how they work.
I’ve upgraded to SCOM 2016 UR6 and confirmed KB4459897-AMD64-ENU-WebConsole.msp installed correctly for the Web Console, but MP 7.0.0.64 still shows it as Web Console UR Level = 2016 UR5. I’ve left it all day but it’s still the same.
Cheers
Steve
Sorry, forget that – a reboot was all it needed! Thanks!
Great work Kevin, maybe you could add a task that can update the workspace key for a Log Analytics workspace. (aka remove and add with the new key in one step)
Would you want it to wipe out ALL existing workspaces, or remove one, while adding one? Some customers multi-home to multiple workspaces…. so the two step process is “safer” unless you want a task that literally removed one by the ID, and adds one by the ID.
Awesome MP as always Kevin.
Would you be able to incorporate Server Description as well:
I am interested in showing Servers “Description” in SCOM either from Active Directory and/or using the Servers “Computer Description” field from the server itself?
Ideally would like to show this info in the Active Alerts, Windows Computers and Discovered Inventory Views as a new Column.
Also if this could be present in the Windows Computer properties of “ServerXX” Detail View under Windows Computers.
I would like to have this available for all windows servers /computers either in or out of Domain.
If you can help me project both Description from AD and from the Server itself in its own column each would be much better to compare and standardise this info in both areas.
or if its easier to make the Servers Description field as default and if that is blank it should show the Description from AD.
Hope there is an easier way to get this info into SCOM.
We use the AD description as our CMDB. I created a task that runs this to pull the AD description from inside SCOM.
Command line task
Application = powershell.exe
Parameters = Get-AdComputer -Identity $Target/Property[Type=”MicrosoftWindowsLibrary7585010!Microsoft.Windows.Computer”]/NetbiosComputerName$ -Properties * | Select-Object Name,enabled, Description
hi,
Is there any risk to import this management pack as is?
Most people do just that. However, if you use scoped views and limit what tasks your users can run, you generally won’t approve some of these tasks as they allow non-administrators ability to run tasks on agents as local system, which is technically an elevation of privilege. This is why you should never grant all users all tasks. Other MP’s work the same way with any agent tasks.
Is there an easy way to publish all the views in this MP only for the Administrators? After importing this MP operators can se and run tasks…
Can anyone suggest me what can i use to monitor servers from untrusted domain, GW or seperate MS in untrusted Domain and which one will be better and Why ?
What all the difference we get in terms of the performance if we use GW or MS ..
Please help and suggest…
You never place a management server in an untrusted domain.
Is it possible to edit the XML for this MP so that views and tasks only will be exposed SCOM Administrators?
No. However, when you scope access to the console for non-admins – you should be choosing what views and tasks are available to your users.
Ok but when i am trying to change that under User Roles and properties on operators etc, it is greyed out and i cant edit anything there.
Ok i think i got it now, i have to create a new User Role to be able to choose what to scope… I made a new User Role based on Operator and under Dashboard and Views i choosed “Only the dashboards and views…” Marked everything and unmarked “SCOM Management views”… I guess that the Task pane is dependent on the Monitor Tree, so did not choosed anything there?
Hi Kevin, Thanks for the MP. I like the useful features (Agent version, Action Account, PS Installed…). I landed on this MP while needing to determine if the APM is installed. However, if I Repair the Agent and untick the box to keep or install APM, the State View reports as true. I’ve uninstalled the agent entirely and installed it without APM but the State View in SCOM Agents shows true. Even after using the “Execute any Powershell” and the NOAPM=1 command it shows as true. I’m having trouble using this to determine the install state of APM and cannot seem to produce a false for APM Installed.
Do you have any idea as to what could be happening to show all of the properties as true regardless of the install state? Or, why all of our APM Installed are true?
So, it turns out that the APM agent is installed even if the box is unticked to “keep or install APM”. Even on a clean install, the APM agent is still installed. The only difference I noticed is the Startup Type for the “Microsoft Monitoring Agent APM” service to either Disabled or Automatic depending on whether or not the “keep or install APM” box is ticked.
Even though APM is “not installed” (installed but startup type set to disabled) the “SCOM Agents” State View still shows the APM Installed as True. Perhaps a better property to show would be if the Startup Type for the Microsoft Monitoring Agent APM service as Automatic for Disabled.
Even though APM is “not installed” (installed but startup type set to disabled) IIS still grabs the profiler service after rebooting the server. Catch-22.
This is by design.
Installed means installed. It doesn’t matter what the service looks like. The purpose of not installing APM is that the binaries are service are not installed at all. If yours is installing APM, even with the box unchecked – something is wrong.
Thank you Kevin!
Indeed; something was wrong. Everything was at 1807 except the Management server, found to be 1801. Once I brought the mgmt server to 1807 everything worked as intended. I uncheck the APM box during Install or Repair and APM is not installed!
The hardest part of inheriting a system is not upgrading, but rather assuming that everything is the way it should be.
I have tried to delete one greyed out agent (agent already uninstalled) using Agent – Delete task but i am getting below error so does that mean without agent we cannot delete?
Health Service ‘server.com’ in which the location monitoring
object is contained is not available. Make sure that the computer hosting the Health Service is
available and verify that the Health Service is running.
What’s the powershell to query the agents if there’s a OMS workspace or not? I cannot figure it out and it would be much appreciated !
We havce about 2000 agents. When we try to open the SCOM Agents view, the console become unresponsive for a long period. When it finally displays the agent list, it’s not possible to scroll or mark agents. Is this a known problem. How can we fix it?
Thanks in advance
I don’t know why this MP view is so slow to open. I think it has something to do with the number of properties and total length of each property. This view is slow to open in any large environment.
Try creating a view in My Workspace, and scope it to the “SCOM Agent Management Class” and see how it opens there.
One thing that helps is a nightly reindex of the OperationsManager database. Are you doing that?
Thanks for the feedback. I will try creating a view in My Workspace and see how it turns out. We are running nightly reindexing of our OM database.
I just imported the 10.19.10311.0 version. When I view it in the Web Console I’m not seeing a column with the Agent Device names. The column starts with the Agent Version. Is this an oversight, or am I missing something somewhere?
Hi Wil,
I never test with the web console. I repro your complaint…. I will look into it and see if there is a simple change I can make to resolve this for web console users.
Hi Kevin, we’re not using system as default action account on DCs. (This is to prevent SCOM admins becoming Domain Admin by deploying malicious script rules). For this MP, the SCOM.Management.Agent.Class.PowerShell.Properties.Discovery doesn’t work. It can’t access the “Health Service State” folder to read the “OpsMgrConnector.Config.xml” for the failover MS. Do you have any solution? An alternative way to get this data or a generic way to change the ACL of the HSS folder automatically (even if we remove this folder in the future)?
You’d need to add a runas account and profile to this MP, and all workflows, to leverage a privileged account. Or, you’d need to allocate the necessary rights to each area that’s failing to your default action account.
The Health Service State folder has inheritance disabled for ACLs and only allow access to SYSTEM and Administrators. On DCs we can’t allow a custom rule running as SYSTEM or as a member of Administrators.
I’ve currently modified the ACL on the HSS folder to allow read access for an action account. But if we remove the HSS folder to clear the cache in the future, the ACL is gone as well. We will have to add it again manually.
I had to do the same for the AD integrated discovery: I had to modify the ACL of a regkey of the healthservice service.
In an ideal world, SCOM would set these ACLs automatically based on a profile.
Apparently this is fixed in SCOM 2019. The agents on our DCs were still 1801. We’ve just upgraded from 1801 to 2019 UR1.
I don’t have to modify the ACLs anymore, the inheritance stays enabled now.
Hello,
Great MP
just a suggestion to get some more Information about the Computers, will it be possible to collect this information in your MP an display them :
What other data do you want?
The tasks no longer show for this marvelous Management Pack. We have a brand new SCOM 2019 system and everything was good until I saw that I had used the SDK account in place of the Action account when creating the Management servers. I decided to correct that error by changing the SDK to the Action account in the “Default Action Account” Profile. I BELIEVE that’s when the tasks vanished. All other system components are working right, and the Discovered Properties for this MP are good. So two things, did I cause this damage by changing the Default Action Account, and is there any way to recover? Both the SDK account and the Action account I changed to are domain accounts with full Administrator authority. Ah yes, one more thing. If I try to change the Default Action Account back to the SDK account, it crashes the SCOM console, so I have a one way road apparently.
You cannot just change accounts like that, because of SQL permissions.
In order to change the account used for the default action account on management servers, you need to:
Make sure the MSAA (Management Server Action Account) has Local Administrator on every management server, and has the correct permissions in SQL:
https://kevinholman.com/2019/03/08/scom-2016-security-account-matrix/
GM Kevin. Thank you for that link on SQL permissions and the Default Action Account. It was invaluable and everything is running clear again. I noticed that the link said the values are not really applicable for SCM 2019. But they seemed to map well nevertheless.
As usual, GREAT MP! 🙂 Thank you so much for all your tips and tricks!
Couple of new task tos enhance the MP to help remove agent.
* Identify grey agents and HB failure more effectively to flush and restart agent.
* Stop agent and disable auto-start. This way agent won’t pop back up in pending is the agent is still running.
Tell me more.
What do you mean in more detail on the first one, or how would that look for the first one? The HealthServiceWatcher view shows you agents that are critical and most likely that’s heartbeat.
On the second one, what’s the scenario where we would want to do that? Why not simply uninstall the agent?
Do you know of a way from command line to add a Management Group for Dual Homing? I am running the agent install based on https://docs.microsoft.com/en-us/system-center/scom/manage-deploy-windows-agent-manually?view=sc-om-2019 and it completes the install but the new Management Group doesn’t show up.
You cannot add a new management group during an agent upgrade. You can assign a single management group during a fresh install.
I have script examples of how to add a management group:
https://kevinholman.com/2017/05/09/scom-management-mp-making-a-scom-admins-life-a-little-easier/
https://kevinholman.com/2018/06/12/how-to-multihome-a-large-number-of-agents-in-scom/
Old: https://kevinholman.com/2014/01/29/using-the-agent-scripting-objects-on-a-scom-2012-agent/
Thank you!
Thank YOU, Superman.
Hi there,
I’m trying to use the execute any powershell component of this MP via script, but not having much luck…I must be missing something simple…hopefully…code is as follows….hoping you have the answer!!! Thanks!!!
$instance = get-scomclass -DisplayName “Windows Computer” | Get-SCOMClassInstance | ? { $_.DisplayName -like “servername” }
Start-SCOMTask -Task $task -Instance $instance -Override $overrides
Start-SCOMTask : The task cannot be executed against the object(s) because the target of the task does not match any of the classes of the object.
At line:1 char:1
To answer my own question…the SCOMClassinstance object somehow is not of the right type for being passed to the $instance parameter of the Start-Scomtask cmdlet. I tried using Get-SCOMMonitoringObject instead, which doesn’t provide a unique value, but rather a list, but using the object in that list that had the same properties as the get-scomclassinstance output, I could pass this on to start-scomtask and it worked. That is a little strange because both results are of the same class, namely Microsoft.EnterpriseManagement.Monitoring.PartialMonitoringObject
I guess I can work with that…just not quite as elegant as I had hoped. Maybe there is a better way to achieve the same thing but will keep going with this for now.
cheers
Eric – you simply need to provide a a class and instance that the original task actually points to:
$ServiceName = “Spooler”
$TaskName = “Demo.Example.RestartService.Task”
$Task = Get-SCOMTask -Name $TaskName
$Class = Get-SCOMClass -Name “Demo.Example.Class”
$Inst = Get-SCOMClassInstance -Class $Class | Where {$_.Path -eq “servername.domain.com”}
$Overrides = @{ServiceName=$ServiceName}
Start-SCOMTask -Task $Task -Instance $Inst -Override $Overrides
Running a SCOM task, however, should generally be done pointing to a management server, and running the Powershell there. Not an agent.
Hey Kevin! Thanks heaps! Have got this going now!
With regards to the pointing to a mgmt server, earlier on in the code I am using this
Sorry I hit the post button by mistake somehow…anyways…I am using this line earlier in the code if that’s what you meant about the mgmt server.
New-SCOMManagementGroupConnection $mgmtServer
Cheers!
Hi Kevin,
I’ve checked “Don’t prompt in the future…” in Task Confirmation (Management Group – REMOVE task).
How can I uncheck it back now?
Hi Tomas
Open Regedit: Computer\HKEY_CURRENT_USER\Software\Microsoft\Microsoft Operations Manager\3.0\Console\
Search in one of the IDs for a REG_DWORD with Value 0 and set it to 1.
Hi Kevin, I have this strange issue: the task “Execute any PowerShell” is immediately executing a code, preventing me to add the override. in fact, I cannot see the Override button, because a script immediately start. How can I revert to a normal status, where I still have the Override button ? Thanks
Pingback:Easily Configure SCOM Cross-Platform Management Server Certificates - The Monitoring Guys
Hello Kevin. When importing the .xml I received an error regarding line 2857: $SqlConnection.ConnectionString = “Server=$SQLServer;Database=$SQLDBName;Integrated Security=True”.
The characters enclosing the SQLConnection string are “ but should be “.
Besides that, great MP, been using it for a long time now.
Thanks! Fixed!
Hi Kevin. When importing the .xml (10.19.10407.1) I received an error :
”
This management pack cannot be imported.
: XSD verification failed for the management pack. [Line: 50, Position: 90]
‘>’ is an unexpected token. The expected token is ‘=’. Line 50, position 90.
”
When I try to fix the .xml file, it displays more other errors. Can you check on github
I just tested import on SCOM 2012, 2016, and 2019. There are no errors. Are you downloading from the “CODE” > “Download Zip” or are you trying to copy/paste from the XML in Github screen?
Hi Kevin,
Can you please implement some of these Tasks in your MP… https://gallery.technet.microsoft.com/SCOM-Task-Collection-00b25311 and https://gallery.technet.microsoft.com/Find-Disconnected-User-on-867961a3 ?
It would be great to have one MP to rule them ALL 🙂
Pingback:SCOM – How to remove “don’t prompt when running this task in the future” flag from “Execute any PowerShell” task. – Tech Corsair
Hi Kevin,
I just created a task for pending agent approval (I’m using it to delegate the agent approval to non-admin users in an environment where we don’t want auto approval.)
I was considering releasing the MP on its own, but it would probably make more sense to integrate it in your MP if you’re interested…
Basically :
– A “Pending approval” view, targeted at Microsoft.SystemCenter.UserActionManager and with PendingStateType = 0 (manual agent install)
– An “Approve pending agent” task with a powershell writeaction that simply runs Get-SCOMPendingManagement | where {$_.agentname -eq “TargetDevicePrincipalName”} | Approve-SCOMPendingManagement
That’s a really good idea. I haven’t updated this thing in a while
Added to the latest release.
Well that was quick!
Hi Kevin, we would like to use this feature for the same reason above, however the agents in our environment are connected via gateways that reside in external domains. The approval script runs with the default action account of the gateway, which in our case doesn’t have permission to approve. The user obviously doesn’t have permission as they are not admins. Is it possible to change the Run Location or specify another Run As account?
question on this MP. i have it loaded and it is awesome, but on the SCOM Agents pane, under Update Rollup i actually see a version number 10.19.10140.0 vs seeing 2019 UR1, etc….
then under SCOM Servers, under Server UR Level i see 2019 RTM but im actually running UR1. i can see under Administration\Operations Manager Products\Management Servers listed as “Update Rollup 1 Patch”.
any ideas? thanks as always.
Hi,
I installed this MP and it seems that I can’t see any agents in SCOM Agents view. But in Administration – Agent managed I have 8 healthy devices.
Anyone else came across same issue?
“Log Analytics Workspace – ADD” task does not actually add 2019 servers to ATP console. It only works on 2012-2016. Would be great if this was fixed. Thanks!
Pingback:Community round up January 2021 | SquaredUp
HI Kevin,
Would there be a opportunity to add a task to write to a registry key? Thanks!
Absolutely. Technically – you could just write a PowerShell script and execute any PowerShell task. but give me an example of something you’d like to write.
Hey Kevin,
is there a way to send the output of the “Execute any PowerShell” into a logfile?
Best regards,
Henning
Hi Kevin,
You implemented a recovery task on the SCOM EventLogSecurity Network Service Elevation of Privilege Monitor. Could it be possible to have the recovery script available as a task so that it can be launched against multiple targets ?
I tried to use the Execute any Powershell task but it looks like it only accept a one-liner script and I didn’t manage to provide the script used in the recovery.
Thanks for your help (and great MP)
Hi Kevin,
we habe trouble with DCs going to mainenance in the background.
In the past we had a lot of trouble with heartbeat failure of a couple of hundred systems, because DC was not available. The change took to long after DC wasn’t available any more 🙁
Can you implenet a row under SCOM Servers with the currently used DC like this?
$Domain = $env:userdnsdomain
$GetDC = nltest /dsgetdc:$Domain
$DC = $GetDC | Select-String -Pattern “DC: ”
$DC = ($DC -split(“: \\\\”))[1]
And maybe a script to change to another DC from another SCOM management server than the one it is connected to?
So it’ll be poosible to change DC manually before it’s going to mainenance
… DC switch with
nltest /Server:ClientComputerName /SC_RESET:DomainName\DomainControllerName
Thx
Michelle
I use Execute any Powershell and Execute any Service Restart a lot but the trouble is that they are targeted to the SCOM Management class. It would be great to have them targeted to Windows Computer so they can be used in views with specific servers or alerts. The Operator role is restricted to what views and tasks they can see. Or even a mini pack with just those 2 tasks.
Thanks
Hello Kevin,
I have Service Manager 2019 in my environment, and it already has a “SCOM” client but in a version 10.19.1035.0 (System Center 2019 Service Manager RTM).
two questions:
– your MP by default brings the version of SCOM 2019 RTM, so far, ok.
– – I don’t know, have you already tested to remove the SCSM agent and put the SCOM 2019 agent, have you already done this test?
Thank you very much
Rodrigo
Hello Kevin,
Hotfix for UR3 has been release by Microsoft. KB5005527 is available here : https://support.microsoft.com/en-us/topic/system-center-operations-manager-2019-hotfix-oct-2021-f5aa7ec5-85c2-4886-b13b-288fd9900737
After applying the fix, Agent are in version 10.19.10185.0 and MS in version 10.19.10552.0.
Will you provide an update for your SCOM Management pack to take these versions in account ?
Thank you very much
Tristan
Update added to support this
Thanks for maintaining this. I noticed that its not picking up the KB5005527 on the gateways.
Oops – I knew I forgot something. I’ll add that tomorrow. Thanks!
Hi Kevin, I think the Hotfix for the Agent still is not being recognized. MS and GW are fine.
I just uploaded an updated version that covers agents and GW.
This has been fixed in the latest version
Hi Kevin,
after updating our MOM Agents to 10.20.18053.0 we get the SCOM EventLogSecurity Network Service Elevation Warning. We have SCOM 2019 UR3 installed and that should include the KB4601269 if I am right.
I guess this is an outdated warning in your Mgmt Pack and can be ignored, right?
Thanks
Full Warning:
“This monitor inspects the Operations Manager Event log security access, and is unhealthy when Network Service is detected to have a high level of priviledge.
The monitor inspects the registry at HKLM:SYSTEM\CurrentControlSet\Services\EventLog\Operations Manager\CustomSD
If the string (A;;0x3;;;NU) is found, this means Network Service has a high level of rights and should be removed per KB4601269.
See:
https://support.microsoft.com/en-us/topic/update-for-event-log-channel-in-system-center-operations-manager-2019-kb4601269-19bfccbe-dbda-1371-9871-f2a32157028a
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2021-1728“
10.20 is an Azure MMA agent. I do not know if those include the fixes for the event log security issue.
Pingback:Top 5 SCOM community recommendations: November SCOMathon Newsletter - SCOMathon
Hi Kevin
We notice an issue where we don’t have the configuration for the PrimaryMS and FailoverList for agent that we have moved the Health Service State Folder.
We adapt your script by getting the value from the
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\HealthService\Parameters\State Directory instead.
Ouf DSE (Larry Leblanc) wrote you an email on that situation with the code correction to implement 🙂
thanks and great job on this MP !
Hi Kevin,
Imported your Management Pack yesterday and it seems since then I can´t get my TASKS to show up in the SCOM Console on the Server, but they show up in the webconsole.
Removing your MP has brought them back in the console now.
Are there any issues with SCOM 2019 UR3?
thx and best regards
Geri
Pingback:Coffee Break: Deep dive into a SCOM Administrator's toolbox - SCOMathon
Kevin, I updated from v10.19.10505.0 to 10.19.10552.1 in hopes of resolving a issue. When I view SCOM Agents under SCOM Management and select to add the column “State”, all of the agents display as Not Monitored. When I select the next item down, SCOM HealthService, all the agents show healthy. Any idea what may be going on here.
Environment: SCOM 2019 UR3.
Thanks as always,
Tony
EMAIL *
WEBSITE
Pingback:The best free SCOM Management Packs you can download today - SquaredUp
Hi Kevin in SCOM 2018 CU1 how to enable VMWare horizon VDI monitoring
Hi Kevin, thanks for the awesome work on this MP. We use this on a regular basis and it helped us a lot so far. We maintain a total of 8 management groups with round about 5.000 Windows servers and 5.300 Linux servers.
Maybe as an enhancement request for the future: would it be possible to add an additional view for Linux agents? Maybe with information about agent version (and mapping to which RTM/UR version it belongs) and rpm packet version of scx/omi and if available the installed modules like apache/mysql. Also the OS+Version and the assigned resource pool could be interesting. Which pool member currently manages the agent would also be great to know, but I guess that is something hard to put into that.Just a few thoughts….
Thanks,
Holger
Kevin – Agent task that leverage the ComObject
Example: $AgentCfg = New-Object -ComObject AgentConfigManager.MgmtSvcCfg
Cause: Event ID 4000 HealthService
A monitoring host is unresponsive or has crashed. The status code for the host failure was 2164195371.
The script does not cause this running script manually or course….
I did try just having it perform “Get” rather than add / remove… and id still causes the reset….
Just wondering if you saw this in your lab
Pingback:The best free SCOM Management Packs you can download today - SquaredUp DS
It looks like I’ve broken the “Execute software from share” task, It no longer asks for the path for the software one wants to execute. I’m trying to find if I set an override somewhere but not having much luck. thank you for everything.
You can delete the HKCU\Software\Microsoft\Microsoft Operations Manager\3.0\Console key to delete all your personalizations, including this task personalization setting to not prompt.
Pingback:Delete PKI certificates - Kevin Justin's Blog
Is there a way to export the SCOM agent list to an .csv file?
Sure. Get-SCOMClass -DisplayName “Agent” | Get-SCOMClassInstance | Export-Csv -Path c:\temp\SCOMAgents.csv -NoTypeInformation
Pingback:Troubleshooting System Center Operations Manager, Part 1: Troubleshooting the Windows SCOM Agent | POHN IT-Consulting GmbH
How to monitor the scom agent greyed out?
Hi Kevin,
I get the following on a SCOM 2022 UR2 agent when trying to execute the “Management Group – REMOVE” task.
Task Starting. Running as (nt authority\system)
Removing Management Group (ITOP)
ERROR removing Management group. Error is: (Value does not fall within the expected range.).
What could the issue be? It shouldn’t harder than just entering the management group name that you want to remove right?
Kevin, I see you’ve updated it 2 months ago to ver:
10.22.10684.0 – Added support for SCOM 2019 UR6. Added support for post UR hotfixes KB5029601, KB5029512, KB5028684, KB5033752, KB5037360
I guess that all newer versions such this one, also supports older update rollups, such as UR4 for 2019?
Thanks Kevin!
yes
Hi Kevin, an official update for 2022 UR3 would be much appreciated. Thanks for your great work.
Yes Kevin. Update for UR3 along with an update to handle Windows 11 Operating system as well.
Both of these have been completed.
Thanks Kevin. Getting this error when I try to import the latest 10.25.10132.5 version.
This management pack cannot be imported.
: XSD verification failed for the management pack. [Line: 25, Position: 76]
‘>’ is an unexpected token. The expected token is ‘=’. Line 25, position 76.
Ignore, its sorted. I downloaded the wrong xml.
We have a SCOM 2025 farm and we installed it new so we have our agents dual-homed between the old farm and the new. I’m trying to use the management pack to remove the old management group from the agents so we can retire the old farm. I invoke the “Management Group – REMOVE” task using an account that definitely can logon to the servers whose agent I’m trying to modify but I get the error “Logon failure: the user has not been granted the requested logon type at this computer. Error Code: -2147023511 (Logon failure: the user has not been granted the requested logon type at this computer).” What is wrong here? Thanks for this management pack, it is so helpful.
This is expected. When you put in an account (which you should not, more on that later) then that account MUST be granted log on a service on EACH agent you want to run a task on. This has been required since SCOM 2019. https://kevinholman.com/2019/03/14/security-changes-in-scom-2019-log-on-as-a-service/
What you should do with almost all tasks, is NOT supply a credential. Let the task run as the default agent action account, which is Local System. That has rights to make changes on the agent managed computers.
I believe this is a bug in SCOM.Management 10.25.10324.0
I have just updated from SCOM 2022 UR2 to UR3
If i look in Monitoring\SCOM Management\SCOM Server
– Server Version + Consol Version show 10.22.10.118.0 = 2022 RTM 🙁
– WebConsol Version show 10.22.11642 = 2022 UR3 🙂
If i look in Administration\Operations Manager Products
– Management Server, Operation Consoles and Web Servers, show 10.22.11642.0 = Update Rollup 3 Patch 🙂
I have looked at
Reg-keys:
Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\System Center Operations Manager\12\Setup\Server\RTM_UR Version
Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\System Center Operations Manager\12\Setup\Console\RTM_UR Version
both show version 10.22.11642.0
File version:
C:\Program Files\Microsoft System Center\Operations Manager\Server\Microsoft.Mom.Common.dll
C:\Program Files\Microsoft System Center\Operations Manager\Server\Tools\TMF\OMTraceTMFVer.Dll
C:\Program Files\Microsoft System Center\Operations Manager\Console\Microsoft.MOM.UI.Components.dll
all show version 10.22.11642.0
So I have not been abel to find the Bug. I can only see it in the console
Thank you! You are correct and I have uploaded a fixed version to github.
Love this MP, but I’ve been tearing my hair out thinking my UR1 Hotfix has not been applying until I found that SCOM.Management 10.25.10603.0 has the wrong file product version for MOMConnector.dll.
MP script: “10.25.11168.0” {“2025 UR1 with KB5080648”}
MOMConnector.dll post-KB5080648 downloaded March 27, 2026: 10.25.11182.0
I updated the discovery script manually and now see the correct versions in the console again.
DAMN! The MSFT product group strikes again. They gave us a copy of KB5080648 to test and evaluate, which is what I built the MP on. Then they obviously changed the version of the file before releasing using the same KB number, and didn’t tell us. This stinks, because we need to test it all again.
Ok – I updated the MP to include the more recently published version of KB5080648
Hi kevin,
SCOM Management pack version which i have is 10.22.10610.0 and the connection tab in SCOM agents under SCOM Management is empty. Do i need to make some changes for it OR do i need to install the new version of this MP. Please suggest
Connections is always blank by default. You can input the servers by editing the XML for this – in the script. This is to test firewall access from agents to potential failover targets.
I document the functionality here: https://kevinholman.com/2018/10/13/how-to-determine-if-your-agents-are-firewalled-from-specific-management-servers/
Thank you so much. I have edit the script. In my environment lot of different domains and each domain having domain scom gateway. So can i edit in script like if the domain is xy, then it should test the connection with that xy domain scom gateway?