There are several examples in blogs on how to create a generic text log rule to monitor for a local text file (Unicode, ASCII, or UTF8).
This will be a step-by-step example of doing the same, however, using this to monitor the log file on a remote UNC path instead of a local drive. This is useful when we want to monitor a file/files on a NAS or an a share that is hosted by a computer without an agent.
This is a bit unique… instead of applying this rule to ALL systems that might have a specific logfile present in a specific directly – we are going to target this rule to only ONE agent. This agent will monitor the remote fileshare similar to the concept of a “Watcher Node” for a synthetic transaction. Therefore we will be creating this rule disabled, and enabling it only for our “Watcher”.
In the Ops console – select the Authoring pane > Rules.
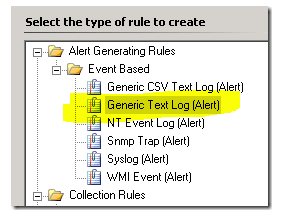
Right click Rules, and select Create a new rule. We will chose the Generic Text Log for this example:
Choose the appropriate MP to save this new customer rule to, and click Next.
For this rule name – I will be using “Company Name – Monitor remote logfile rule”
Set the Rule Category to “Alert”
For the target – I like to use “Windows Server Operating System” for generic rules and monitors.
UNCHECK the box for “Rule is enabled”
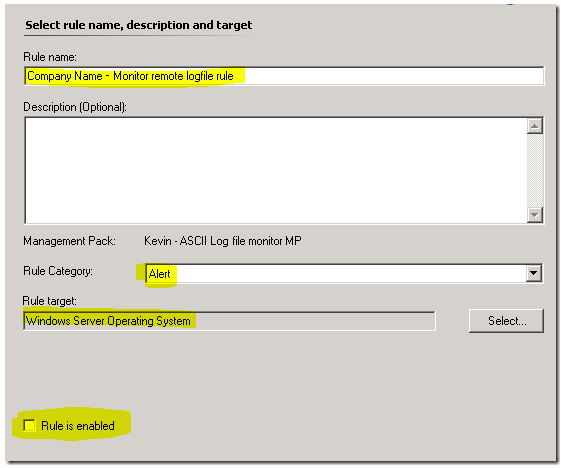
Click Next.
The directory will be the UNC path. Mine is “\\VS2\Software\Temp”
The pattern will be the logfile(s) you want to monitor. We can use a specific file, such as “logfile.log” or a wildcard, such as “*.log”.
You should not check the “UTF8” box unless you know the logfile to be UTF8 encoded.
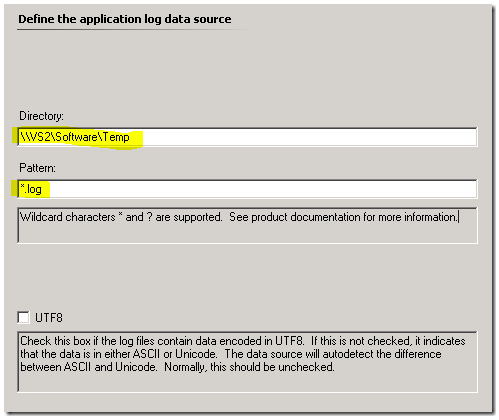
Click Next.
On the event expression, click Insert for a new line. Essentially – log file monitors look at each new line in a logfile as one object to read, and this is represented by “Params/Param[1]” This “Parameter 1” is the entire line in the logfile, and is the only value that is valid for this type of monitor – so just type/paste that in the box for Parameter Name.
Since we want to search the logfile line for a specific word, the Operator will be “Contains”.
For the value – this can be the word you are looking for in the line, that you want to alert on. For my example, I will use the word “failed”.

Click Next.
On the alert screen – we can customize the alert name if desired, set the severity and priority, and build a better Alert Description. If you are using SP1 – the default alert description is blank. If you are using R2 – the default alert description is “Event Description: $Data/EventDescription$” HOWEVER – this is an invalid event variable for this type of event (logfile)…. so we need to change that right away. I keep a list of common alert description strings HERE
For this – I will recommend the following alert description. Feel free to customize to make good sense out of your alert:
Logfile Directory : $Data/EventData/DataItem/LogFileDirectory$
Logfile name: $Data/EventData/DataItem/LogFileName$
String: $Data/EventData/DataItem/Params/Param[1]$
Click “Create” to create the rule.
Find the rule you just created in the console – right click it and choose “Properties”. On the Configuration tab, under responses (to the right of “Alert”) click Edit.
Click the “Alert Suppression” button. You should consider adding in alert suppression on specific fields of an alert – in order to suppress a single alert for each match in the logfile. If you don’t – should the monitored logfile ever get flooded with lines containing “failed” from the application writing the log – SCOM will generate one alert for each line written to the log. This has the potential to flood the SCOM database/Console with alerts. By setting alert suppression here – we will create one alert, and increment the repeat count for each subsequent line/alert. I am going to suppress on LoggingComputer and Parameter 1 for this example:

Click OK several times to accept and save these changes to the rule.
Now – we created this rule as disabled – so we need to enable it via an override. I will find the rule in the console – and override the rule “For a specific object of class: Windows Server Operating System”
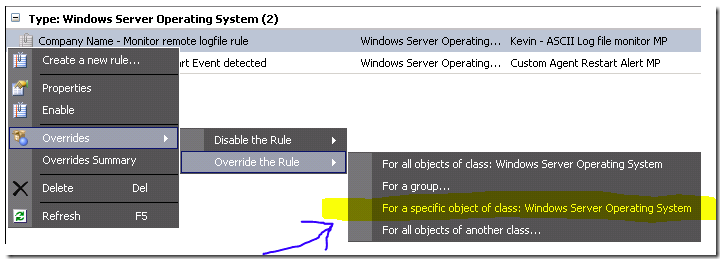
Now – pick one of these machines to be the “watcher” for the logfile in the remote share.
**Note – the default agent action account will make the connection to the share and read the file. In my case – the default agent action account is “Local System” so this will be the domain computer account of the “Watcher” agent which connects to the remote share and reads the file. This account will need access to the share, folder, and files monitored. Keep that in mind.
Set the override to “Enabled = True” and click OK.
At this point, our Watcher machine will download the management pack again with the newly created override, and apply the new config. Once that is complete – it will begin monitoring this file. You can create a log file in the share path, and then write a new line with the word “failed” in it. You need a carriage return after writing the line for SCOM to pick up on the change.
You should see a new alert pop in the console, based on matching the criteria. Subsequent log file matches will only increment the repeat count. Customize the alert suppression as it makes sense for you.
Then – create additional rules just like this – for different UNC paths.


trying to create a simple rule to alert when a number (100) is listed in a log file.
I have used these instructions and it doesn’t create an alert.
Is there anywhere in SCOM that logs when monitors or rules don’t work?
There isnt a log for when something doesn’t match. There is likely some configuration issue causing your log monitor to not work. There is a workflow simulator, that can be used to watch an entry to a log file, then look at the condition detection output evaluating each log.
So wildcards are supported as part of the file name but not in the directory path?
can we add or condition to match two words in a log file? if so should we use Params/Param[1] for second word?
Yes. Param 1 is simply the entire line. You can use Regex to look for multiple strings, or a single long string, or even multiple expressions like (string contains FOO) AND (string contains BAR).
My requirement is to continuously monitor the log file in a server; trigger an alert when any modification occurs on the file.
I got an idea , that we can monitor the date modified and trigger an alert when the file is modified. Could you please help on that.
Thanks in advance.
Do you have to use UNC or can C:\path be used?