So…. with the introduction of Server 2008 into OpsMgr… as a monitored agent, you might need to re-evaluate some of your old rules.
Almost all (if not all) of the basic event ID’s and parameters, in the security event log, have changed.
For instance, I had a rule to alert me on every RDP logon to every server in my lab. I did this on Server 2003, using the following data source configuration:
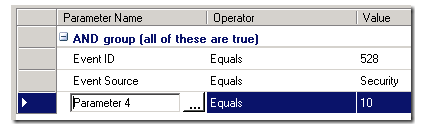
The logon event was 528, I used the Security event source (not really required in this case) and then I only wanted to alert on RDP/Console logon types… so that is where Parameter 4 came in. I had to use LogParser to figure out which parameter is which.
Now – I realized, since I rebuilt my main Terminal Server with Server 2008, this rule isnt alerting anymore.
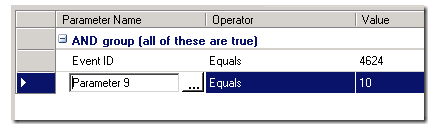
It is apparent that the new security event is now this:

So – off I go to update my rule.
I will use Event ID 4624, that part is easy…. but now – which parameter is the logon type of “10” now?
I can certainly use LogParser… and it will tell me, but in Server 2008 – there appears to be a shortcut: Choose the Details Tab of the event you want, and all the parameters are listed, in order… and you simply have to count down:

Counting down from the top – that is Parameter 9. So my new data source expression for the rule looks like this:
So – I will ONLY get alerts on those specific events. But wait – I need to customize my Alert description! I can use the same “cheat”. In my alert description – I want to state something like “Username logged on to ServerName from IPAddress”. I can get all of that right, and the parameters – right from this event:

Counting down – I can see this is parameter 6, 12, and 19. So I make my alert description look like so:

And my alert?
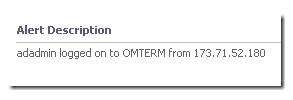
Perfect!
Use this method to quickly figure out which parameters you want for your rule criteria, and your alert descriptions.
UPDATE – 2-25-2009
I have to update this post – based on the comment from Raphael Burri (http://rburri.wordpress.com/)
In addition to the easy way to find out parameters in Server 2008 – he commented on an even better way to bring rich alert descriptions in… without much work.
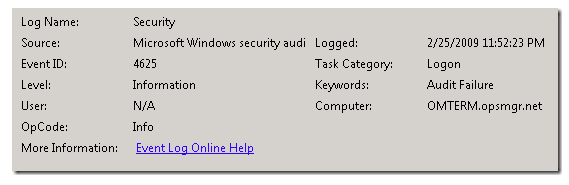
So for this example – I will create a new rule – which will alert me when someone types a bad password while accessing my Terminal Server:
The event in question – has changed from EventID 528 on Server 2000/2003 – to EventID 4625 on Server 2008:
Now – instead of using event parameter numbers in my Alert Description – I will use the event XPath name straight from the event! Open the event… and choose the details tab. Then choose the XML view. It looks like this:

Now – to capture ANY of these “Event Data” fields… we could use parameters – counting down like the example I posted above. OR – we can simply pull the parameter name – which is given to us right from the event:
Simply use this format:
$Data/EventData/DataItem/EventData/Data[@Name=’EventParameterName’]$
For instance… I want my alert description for this alert to state:
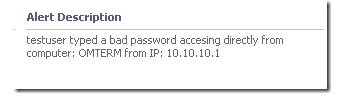
(Username) typed a bad password accessing directly from computer: (computername) from IP: (IP Address)
So from above – I can simply use the “Data Names” listed in the event data:
$Data/EventData/DataItem/EventData/Data[@Name=’TargetUserName‘]$
$Data/EventData/DataItem/EventData/Data[@Name=’WorkstationName‘]$
$Data/EventData/DataItem/EventData/Data[@Name=’IpAddress‘]$
My alert description now looks like this:

The alert comes in as:
Thanks for the tip Raphael!
